Defend Your Business Against the Latest Cyber Threats
Nam libero tempore, cum soluta nobis eligendi optio cumque nihil impedit minus quod maxime placeat facere possimus quo assumenda omnis
Chat With Us+
Worldwideclients
+
Cyber SecurityExperts
%
Retentionrate
Effective Approach for Your Cyber Security
Increased & Evolving Threat
Nam libero tempore, cum soluta nobis eligendi optio cumque quo minus quod maxime placeat
Learn MoreContinuous Monitoring
Nam libero tempore, cum soluta nobis eligendi optio cumque quo minus quod maxime placeat
Learn MoreStructural Weaknesses
Nam libero tempore, cum soluta nobis eligendi optio cumque quo minus quod maxime placeat
Learn MoreWidening Attack Surface
Nam libero tempore, cum soluta nobis eligendi optio cumque quo minus quod maxime placeat
Learn More
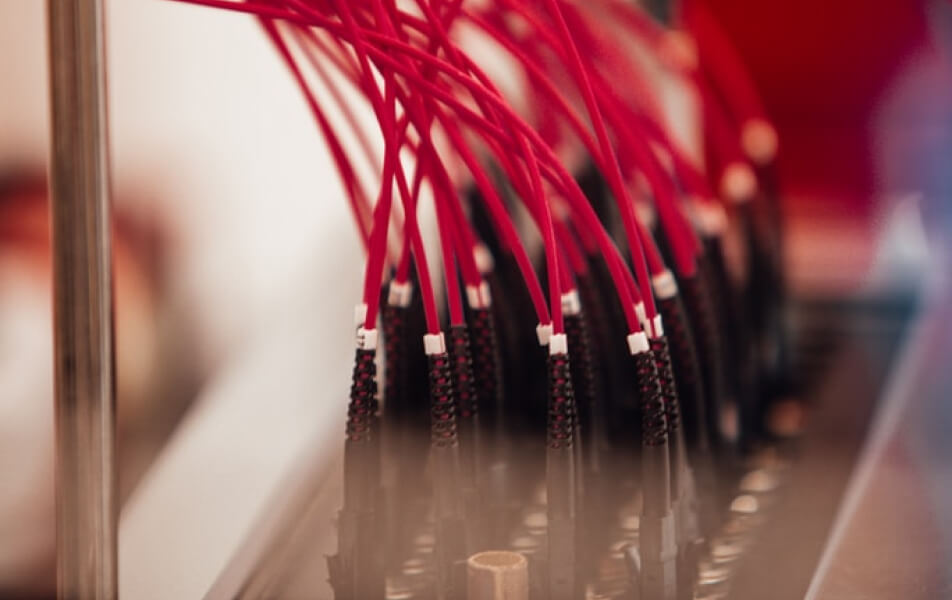
Powerful Cyber Security Operation Center
Nam libero tempore, cum soluta nobis eligendi optio cumque quo minus quod maxime placeat facere possimus assumenda omnis dolor repellendu sautem Temporibus quibusdam et aut officiis nam libero tempore
- Managed Web Application
- Free Delivery Services
- SIEM Threat Detection
- Provide Security Services
- Website Security Services
- Content Delivery Network
- 24/7 Hours services
- Website Hack Repair
- Instant Malware Removal
- Security Management
- Database Security
Become Totally Secured by
Following 3 Steps

Choose Security Package
Nam libero tempore soluta nobis eligendi optio cumque minus quod maxime
Step one
Prepare for Security Test
Nam libero tempore soluta nobis eligendi optio cumque minus quod maxime
Step Two
Get the Result & Solutions
Nam libero tempore soluta nobis eligendi optio cumque minus quod maxime
Step ThreeExpert Team Who Are Behind
the Whole Security
Bijoy K. Chowdhury
Founder & Managing DirectorKalpana Chanda
Founder ChairmanThe Simplest Pricing Plan to
Secure Your Data
$499
Nam libero tempore soluta nobis eligendi quod maxime placeat possimus assumenda
Get started nowPersonal
- Encrypted Transactions
- 24/7 Support Service
- Automated Daily Backup
- Free Hardware Included
- Scan Every 12 Hours
$1099
Nam libero tempore soluta nobis eligendi quod maxime placeat possimus assumenda
Get started nowStartup
- Encrypted Transactions
- 24/7 Support Service
- Automated Daily Backup
- Free Hardware Included
- Scan Every 12 Hours
$1599
Nam libero tempore soluta nobis eligendi quod maxime placeat possimus assumenda
Get started nowCompany
- Encrypted Transactions
- 24/7 Support Service
- Automated Daily Backup
- Free Hardware Included
- Scan Every 12 Hours
Trusted by more than +750 companies around the globe